Introduction to 10.5.50.1
10.5.50.1 is an Internet Protocol (IP) address that falls within the category of private network addresses. It is a part of the IP address space defined by the Internet Engineering Task Force (IETF) for non-public use. Specifically, IP addresses in the range from 10.0.0.0 to 10.255.255.255 are reserved for private networks, making 10.5.50.1 significant for organizations and individuals managing local area networks (LANs) and wider internal networks.
The significance of private IP addresses like 10.5.50.1 lies in their ability to facilitate communication within a private network without requiring a direct link to the broader internet. In this scenario, devices connected to the network can communicate with each other while remaining secure and shielded from outside interference. This ensures that sensitive data is kept within the confines of the organization, which is particularly important for businesses that handle confidential information.
Moreover, using private IP addresses such as 10.5.50.1 helps conserve the limited stock of public IP addresses. Organizations that deploy private IP addressing can use NAT (Network Address Translation) techniques to give their internal devices access to the internet while maintaining a single public IP address. This solution helps mitigate potential issues arising from IPv4 address exhaustion.
In conclusion, understanding 10.5.50.1 is critical for networking professionals, especially as more organizations rely on private networks for security and efficiency. By deploying such IP addresses, businesses can optimize their internal communications while adhering to best practices in data protection.
What is an IP Address?
An IP address, or Internet Protocol address, serves as a unique identifier for a device connected to a network using the Internet Protocol for communication. Acting as a postal address for information packets, IP addresses ensure that data sent over the internet arrives at the intended destination. Each device in a network, whether it be a computer, smartphone, or server, is assigned an IP address to facilitate this communication.
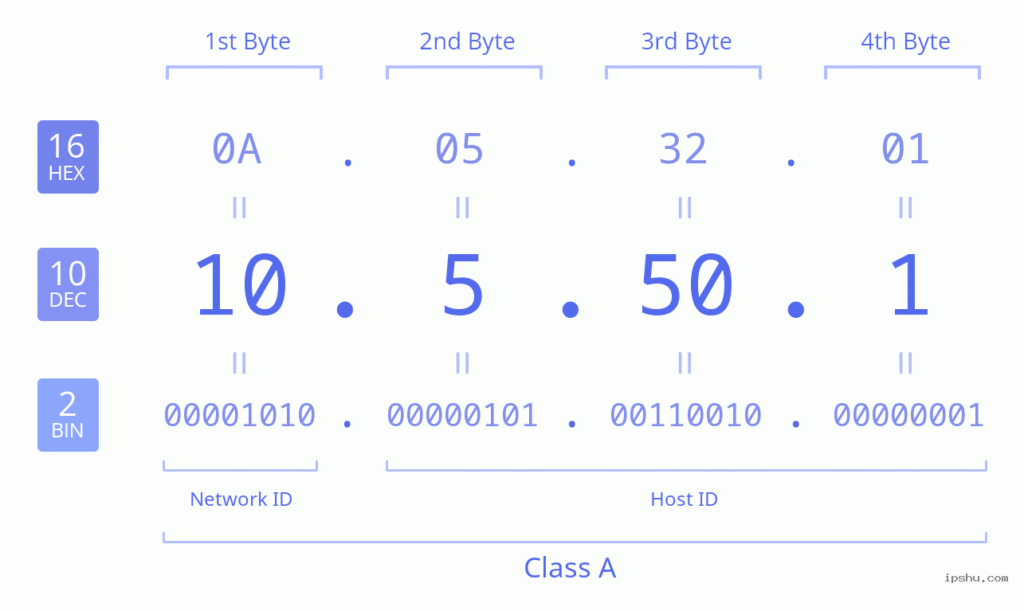
There are two versions of IP addresses in widespread use today: IPv4 and IPv6. IPv4, which stands for Internet Protocol version 4, uses a 32-bit address scheme that allows for a total of approximately 4.3 billion unique addresses. It is written in decimal format, divided into four octets (e.g., 192.168.1.1). However, the rapid expansion of the internet and an increasing number of connected devices have led to the exhaustion of available IPv4 addresses, making the transition to IPv6 essential.
IPv6 is the most recent version of the Internet Protocol, utilizing a 128-bit address scheme. This advancement allows for a staggering number of unique IP addresses—over 340 undecillion combinations. It is designed to accommodate the growing number of internet-connected devices and to improve security and routing efficiency. IPv6 addresses are expressed in hexadecimal format, allowing for a more extensive range of device identification.
In this context, the IP address 10.5.50.1 falls under the category of private IP addresses, designated for use within private networks. Addresses in the range of 10.0.0.0 to 10.255.255.255 are reserved for internal usage by organizations and are not routable on the public internet. Understanding how IP addresses work, including both IPv4 and IPv6, is essential for grasping the foundational elements of network connectivity and the significant role that IP addresses play in the seamless operation of internet services.
The Significance of 10.5.50.1 in Network Configuration
The IP address 10.5.50.1 holds considerable significance in network configurations, particularly in private networks. As a part of the private IP address range defined by the Internet Assigned Numbers Authority (IANA), it is utilized extensively within local area networks (LANs). Devices in a LAN often require an IP address for communication, and 10.5.50.1 serves as a designated gateway for various services and devices, facilitating network traffic management.
In both home and corporate environments, the IP address 10.5.50.1 may be assigned to a router or a gateway device. Within this capacity, it acts as a central point through which all network traffic is directed. This functionality allows connected devices, such as computers, smartphones, and printers, to communicate with one another and access external networks, including the Internet. The use of this specific IP address can simplify the configuration and management of network settings.
Moreover, network administrators often assign 10.5.50.1 for services such as DHCP (Dynamic Host Configuration Protocol) and DNS (Domain Name System). The DHCP service automates the assignment of IP addresses to devices on the network, allowing them to connect effortlessly, while DNS services provide a way to resolve domain names into IP addresses, enabling easier navigation across networks. As a result, the presence of 10.5.50.1 becomes vital for ensuring that devices can promptly acquire network settings necessary for optimal connectivity and functionality.
Ultimately, understanding the role of the IP address 10.5.50.1 within network configurations is essential for both network design and troubleshooting. Proper utilization can enhance overall network performance, leading to a more efficient and reliable communication framework, whether in domestic or enterprise scenarios.
Common Uses of 10.5.50.1
The IP address 10.5.50.1 is primarily employed within internal networks, serving various administrative and operational functions. It is commonly utilized as a private network gateway or default IP address for routers and switches, functioning as a critical point for network management. Organizations often configure their network devices to this address, ensuring that internal resources can be efficiently accessed by all authorized users.
In many corporate settings, 10.5.50.1 acts as the management interface for local area networks (LANs). Network administrators leverage this address to establish secured connections and manage configurations, facilitating a streamlined connection to devices such as printers, computers, and servers. Moreover, the address may serve as a DHCP (Dynamic Host Configuration Protocol) server, providing IP addresses dynamically to devices connected to the network, which enhances network efficiency and organization.
Additionally, educational institutions adopt 10.5.50.1 in their internal networks. This strategic deployment allows for centralized management and monitoring of network traffic, connectivity, and access controls, ensuring that students and faculty members can use the network resources efficiently. In home networks, utilizing 10.5.50.1 is also common, especially in advanced home networking setups that require customization beyond typical consumer-grade configurations.
Overall, the address 10.5.50.1 has become an essential part of many internal network architectures, where it plays a vital role in optimal resource distribution, device management, and providing secure access to users. Its relevance in various environments underscores the flexibility and importance of manageable private IP addresses in modern networking scenarios.
Accessing the 10.5.50.1 Interface
Accessing the 10.5.50.1 administrative interface is essential for configuring your networking equipment, such as routers and gateways. To begin the process, it is crucial to ensure that you meet specific requirements.
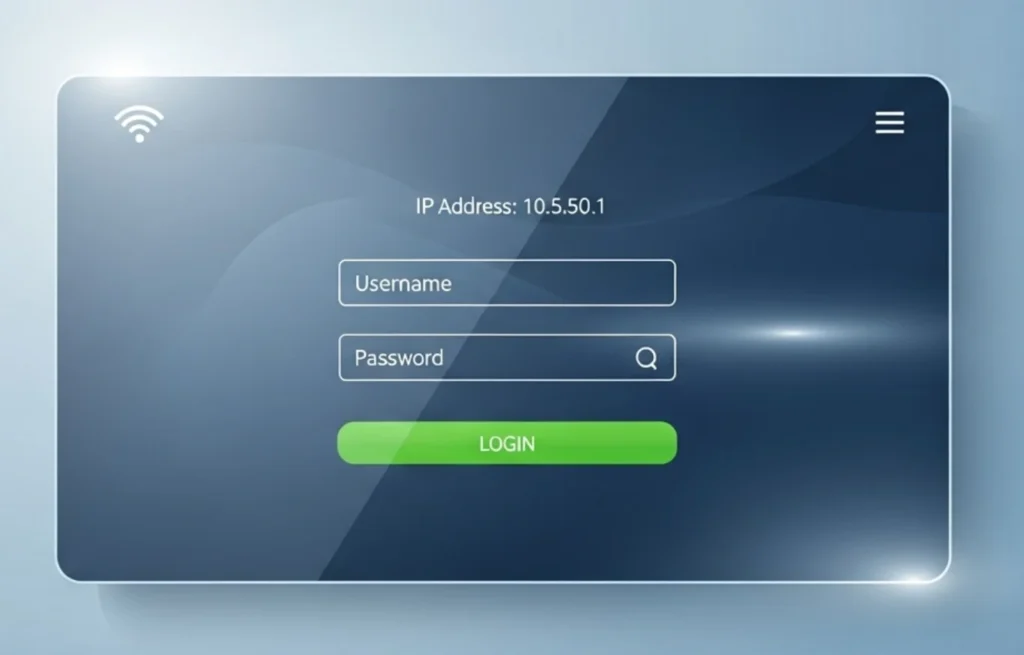
First, verify that your device is connected to the local network where the 10.5.50.1 IP address is utilized. This connection can be wired or wireless, but it is mandatory for successful access. Once you have a stable connection to the network, the next step is to utilize a web browser of your choice. Popular options such as Chrome, Firefox, or Safari work perfectly for this purpose.
In the address bar of your browser, type in the IP address 10.5.50.1 and press enter. This directs your request to the correct gateway, and the administrative interface should appear shortly thereafter. In case the page does not load, ensure that you have typed the address correctly and that your device is indeed connected to the appropriate network. If issues persist, consider restarting your router or checking your network settings.
Upon successfully reaching the interface, you will be prompted to enter login credentials. Typically, this will involve providing a username and password. If you have not changed these from their default settings, consult your device’s manual or the manufacturer’s website for the default login information. Remember that these credentials are sensitive; therefore, it is imperative to safeguard this information after your first login.
Once logged in, you will gain access to a range of administrative tools and settings, allowing you to make necessary configurations to your network. Be sure to navigate cautiously to prevent inadvertently altering crucial settings.
Troubleshooting Connection Issues with 10.5.50.1
Connecting to the IP address 10.5.50.1 can sometimes present challenges for users. These issues may stem from a variety of sources, including network configurations, device settings, or even hardware malfunctions. Understanding the potential difficulties and knowing how to address them is essential for ensuring smooth access to your network management interface.
A frequently encountered problem is the inability to access the 10.5.50.1 address altogether. This could be due to incorrect entries in the browser, such as a typographical error, or because the device’s IP address has changed. To resolve this, ensure that you are typing the correct IP address in the web browser’s address bar. Additionally, you can verify your device’s configuration settings to ascertain that it is set to use the appropriate IP address.
Another common issue relates to network connectivity. If your device is not connected to the network that utilizes the 10.5.50.1 address, you will be unable to log into the interface. To troubleshoot this, first, check the physical connections, such as cables and switches, to confirm that they are securely connected. If you are using Wi-Fi, ensure that you are connected to the correct network and that your signal strength is adequate.
Firewall settings or security software may also block access to the 10.5.50.1 address. Users should examine their firewall configurations and temporarily disable any security software to see if that resolves the issues. Moreover, resetting the router or modem can often clear up persistent connectivity problems. This can be accomplished by unplugging the device, waiting a few seconds, and then plugging it back in.
If issues persist after undertaking these steps, it may be beneficial to consult the manufacturer’s documentation or support resources for assistance. Understanding and resolving connection issues with 10.5.50.1 will significantly enhance your user experience when managing network settings.
Security Considerations for 10.5.50.1
When utilizing the IP address 10.5.50.1, users must prioritize security to protect their network and connected devices. One of the most critical steps in fortifying network security is changing the default password associated with the router or gateway. Default credentials are typically easy for cybercriminals to obtain and exploit, making it essential to establish a strong, unique password. A robust password should contain a variety of characters, including uppercase and lowercase letters, numbers, and symbols, enhancing its resistance to unauthorized access.
In addition to changing the default password, it is advisable to implement network encryption protocols, such as WPA3, to safeguard wireless communications. Using strong encryption helps prevent unauthorized users from intercepting and accessing data that travels through the network. Maintaining up-to-date firmware for the router is crucial; manufacturers frequently release updates that address security vulnerabilities, thus keeping the network shielded from potential threats. Regular checks for firmware updates will ensure the device operates securely and efficiently.
Furthermore, enabling features such as a firewall can provide an additional layer of protection for the network. A firewall acts as a barrier between the internal network and external threats, controlling incoming and outgoing traffic based on established security rules. Users should also consider utilizing network monitoring tools that provide real-time feedback on network activity. Such tools can help detect any unusual behavior or unauthorized attempts to access the network.
Finally, educating all users connected to the network about safe browsing habits and the importance of recognizing phishing attacks can greatly contribute to overall security. By fostering a culture of vigilance and proactive security measures, users can significantly reduce the risks associated with using 10.5.50.1 and ensure a secure network environment.
Comparison with Other IP Addresses
When discussing private IP addresses, 10.5.50.1 is often compared to more commonly used addresses like 192.168.0.1 and 10.0.0.1. Each of these addresses falls within the private network allocations defined by the Internet Engineering Task Force (IETF). Private IP addresses are primarily utilized for local networks, enabling devices to communicate internally without being exposed to the public internet.
The address 192.168.0.1 is part of the 192.168.0.0/16 subnet and is widely used in home networks, while 10.0.0.1 comes from the 10.0.0.0/8 range, which is typically reserved for larger corporate or institutional networks. In contrast, 10.5.50.1 is less common and specifically sits within the 10.0.0.0/8 range, making it suited for certain enterprise contexts where custom addressing schemes are necessary.
Choosing between these IP addresses often depends on the specific networking needs of an organization or individual. For smaller home networks, 192.168.0.1 may be preferred due to its ubiquity and the abundance of consumer-grade routers that default to this address. However, larger organizations might lean towards 10.x.x.x addresses, such as 10.5.50.1, as they provide a broader range of addresses suitable for scalability, allowing thousands of devices to be connected without IP address conflicts.
Furthermore, while both 10.5.50.1 and 10.0.0.1 share the same private designated range, the choice of which IP address to use can also hinge on pre-existing network structures and administrative preferences. The configuration of subnets, security protocols, and the network topology can all influence the decision on which private IP address will effectively serve the needs of the network.
Conclusion and Final Thoughts
Throughout this article, we have explored the significance of the IP address 10.5.50.1 in the realm of network management. As an important address within the private address space, it serves a variety of functions that facilitate the seamless operation of networks, particularly in environments utilizing routers and other networking devices.
One of the key aspects we discussed was the ability to access administrative settings through the 10.5.50.1 IP address. This functionality allows network administrators to configure settings, troubleshoot issues, and manage connected devices effectively. By utilizing this address, users can enhance their network’s performance and maintain security protocols that safeguard sensitive data.
Additionally, we touched on the importance of understanding the context of 10.5.50.1 within the larger framework of IP addressing. Knowing how to utilize private IP addresses enables network managers to design and implement robust networking solutions that cater to specific organizational needs. Furthermore, the private nature of the address ensures that internal communications remain secure, protected from external intrusions.
In closing, comprehending the uses and implications of the 10.5.50.1 IP address is vital for both new and experienced network administrators. By grasping the concepts discussed, readers are well-equipped to apply these insights into their own network systems, promoting efficient management practices and an overall enhancement in network performance. Taking the steps to integrate this knowledge can yield significant benefits, ultimately fostering a more secure and well-managed networking environment.